Dirty Frag represents a dual-CVE vulnerability in the Linux kernel network stack. By exploiting a race condition in IPv6 fragment reassembly, attackers can achieve kernel-mode heap corruption and local privilege escalation.
Est. 4m readRead Article→

CVE-2026-31431, dubbed 'Copy Fail,' allows local attackers to gain root privileges by corrupting the Linux page cache via the algif_aead crypto interface. This article breaks down the technical root cause and the exploitation timeline.
Est. 5m readRead Article→

Setting up Windows 11 on a hypervisor often leads to stuttering audio and slow disk I/O. We followed the official best practices to see if a virtualized workstation can truly replace bare metal.
Est. 4m readRead Article→

Is your HP 920 or 925 scroll wheel jumping or broken? Follow this step-by-step disassembly guide to open your mouse and attempt a repair.
Est. 4m readRead Article→

The HP 920/925 Ergonomic Vertical Mouse feels amazing for medium-sized hands, but poor build quality and a failing scroll wheel hold it back.
Est. 4m readRead Article→

On March 31, 2026, a breach of the Axios npm account led to the distribution of malicious code. Here is the breakdown of the timeline, the actors involved, and the technical bypass used.
Est. 3m readRead Article→

Is the 'Reasoning Wall' actually just a 'Memory Wall'? We explore TurboQuant and the 'Random Rotation' trick that might finally let you run a senior-level AI agent on a single RTX 3090.
Est. 2m readRead Article→

The classic synchronization trap: your backend saves UTC, your frontend displays local time, and suddenly your appointment is two hours off. Here is how to handle time in .NET properly.
Est. 3m readRead Article→

Think .ToUpper() is safe? Think again. We dive into the world of CultureInfo, the 'Turkish I' bug, and why simple string manipulations can crash your production app abroad.
Est. 4m readRead Article→

Part 2 of our local LLM series. We put Qwen2.5-Coder and Llama 3 to the test in real-world agentic workflows on an RTX 3090. Here is why 'mostly working' isn't quite enough.
Est. 4m readRead Article→

Stop sending your code to the cloud. Learn how to leverage an RTX 3090, Ollama, and OpenCode to build a private, lightning-fast AI coding assistant using Llama 3 and Qwen2.5-Coder.
Est. 5m readRead Article→
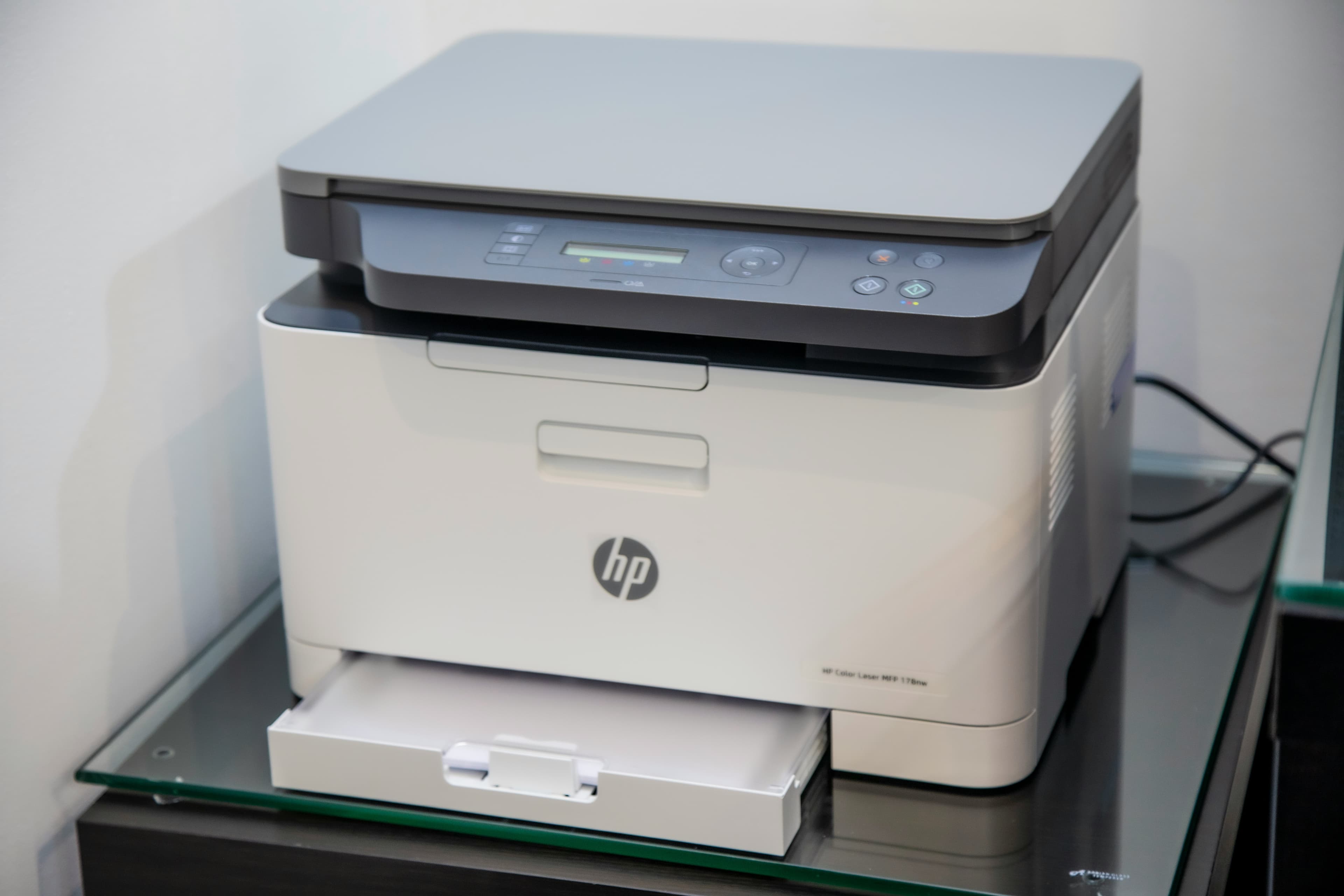
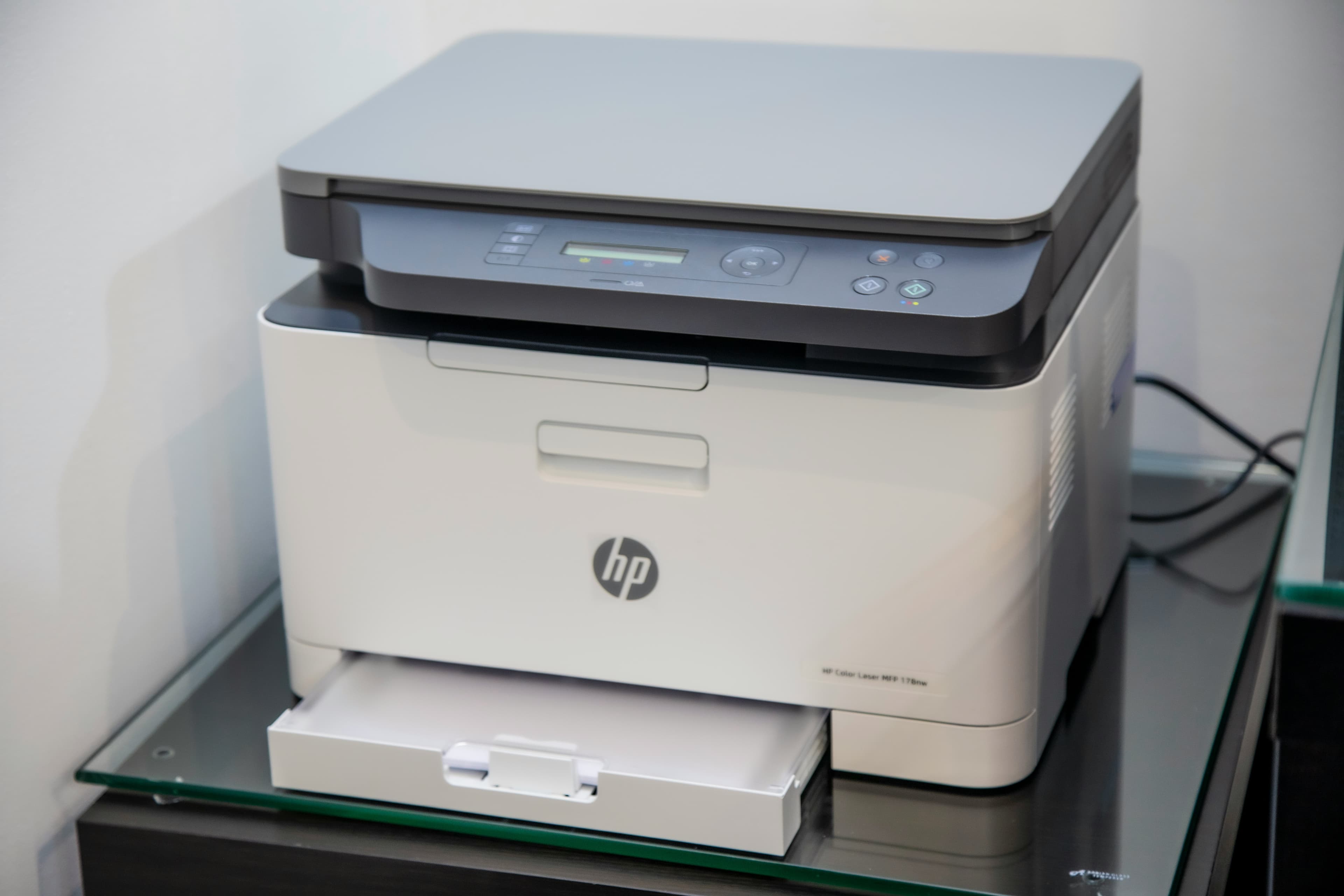
A comprehensive guide to setting up HP DeskJet, OfficeJet, and LaserJet printers on Linux using HPLIP, including wireless configuration and scanning.
Est. 3m readRead Article→
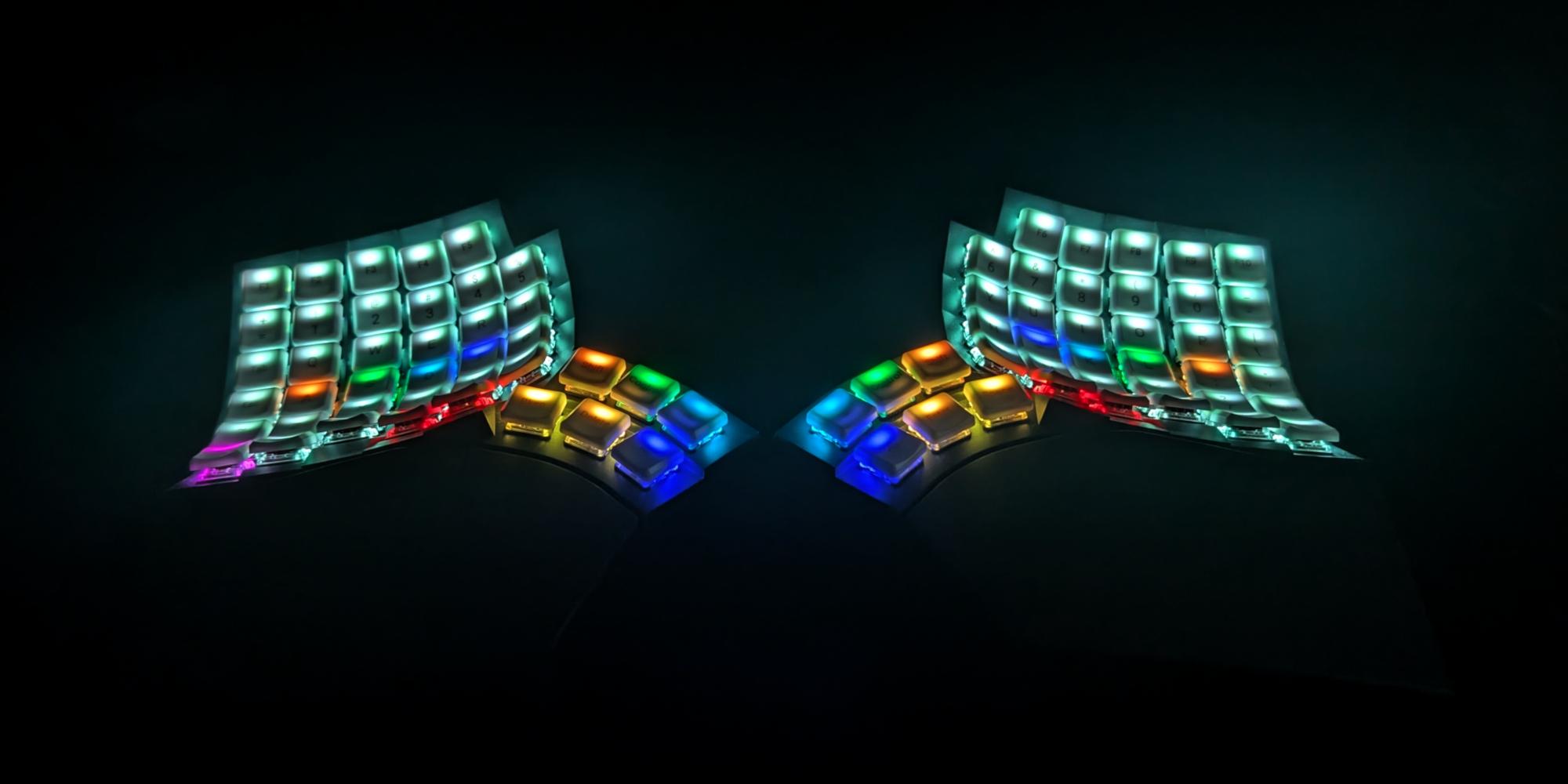
A look back at two years with the Glove80 split ergonomic keyboard. From the initial struggle of learning a columnar layout to the breakthrough of per-key RGB, here is why there's no going back.
Est. 3m readRead Article→

A comprehensive guide on how to build a wireless Ploopy Adept trackball, featuring the highly recommended Any Ball mod, ordering the PCB, and assembling the components.
Est. 6m readRead Article→

OpenClaw is a powerful AI agent, but giving it full host access can be risky. Learn how to run OpenClaw securely with Ollama by leveraging Tailscale to restrict access to a single port, while keeping your home network safe.
Est. 5m readRead Article→

Learn how keyless entry relay attacks work using an SDR and a Raspberry Pi, and discover practical ways to protect your vehicle.
Est. 4m readRead Article→

Trying to control your Raspberry Pi's GPIO pins from inside a Docker container? Here is the quick solution using docker-compose and /dev/gpiomem.
Est. 3m readRead Article→
The Glove 80 is a mechanical keyboard with per-key RGB lighting. In this post we will explore how to set the colors of the keys.
Est. 3m readRead Article→

Pickle Rick room on TryHackMe is a easy Rick and Morty themed room suitable for beginners.
Est. 5m readRead Article→

Explore how to deploy a next.js application on docker hub.
Est. 3m readRead Article→

Explore how to create a next.js blog application with markdown support and static generation at build time.
Est. 6m readRead Article→
In this post we will explore how to with a next.js application to add pages, support routing and dynamic routes.
Est. 5m readRead Article→

In this post we will explore how to create a next.js application using create next app.
Est. 2m readRead Article→

Relevant is a challenging room on TryHackMe that puts you in the role of a penetration tester, tasked with conducting a penetration test and delivering a detailed report.
Est. 14m readRead Article→

Overpass 2 is a hard room featuring a hacked webserver which requires us to retrace the steps of the hacker to gain back access.
Est. 5m readRead Article→

The Internal room on TryHackMe is an hard challenge that let's you slip in the role of a penetration tester, where your objective is to perform a thorough penetration test
Est. 16m readRead Article→

The Daily Bugle room on TryHackMe is a hard room that requires you to compromise a Joomla CMS account.
Est. 6m readRead Article→